
Document Processing with AI Agents: When to Use Bedrock AgentCore Runtime (vs Lambda)
Document processing agent automation Background Intelligent document processing is a pattern we …

AI Isn't a Hammer. That's the Problem | AI Dependency, Deskilling and Critical Thinking
Exoskeleton effect A Guardian column this week asks whether AI dependency is eroding our ability to …
Process large files at scale with AWS Lambda
Multithreading lambda: process large file at scale Background Using serverless technologies like …

Centralised Root Access Management in AWS Organizations: Reducing Risk and Operational Overhead
Centralised Root Access Management in AWS Organizations Background Over the years, we have helped …
Processing over 50 Million Documents with AWS Serverless: An Intelligent Document Processing Success Story
Intelligent Document Processing with AWS Serverless Executive Summary We helped a UK financial …
What is CORS and how to test it
What is CORS and how to test it header image Understanding CORS: Cross-Origin Resource Sharing 1. …

Managing Large IAM Policies: Overcoming Character Limits
Managing Large IAM Policies: Overcoming Character Limits Background While working with AWS Identity …
How to fine-tune the memory for a Lambda function
How to fine-tune the memory for a Lambda function header image Background As a developer, it can be …

How to automate drift detection in CloudFormation StackSets
How to automate drift detection in CloudFormation StackSets Background In this short blog post, …

Applying AWS CDK Guardrails
Applying AWS CDK Guardrails Background The AWS Cloud Development Kit (AWS CDK) is an open-source …

How to Customise the AWS CDK Pipeline
How to Customise the AWS CDK Pipeline Background Have you ever wanted the power of the AWS …

Unlocking the Power of AWS CDK: Why It's Our Default Infrastructure as Code Tool
Querying CloudTrail Logs in an AWS Organization with Athena Background At Virtuability, we’re …
Querying AWS CloudTrail Logs with Athena in AWS Organizations: Setup, Use and Challenges
Querying CloudTrail Logs in an AWS Organization with Athena Background Over the years, we have …
Boto3 and Python unittest.mock
I start this post by saying I’m not a professional software developer, I work mainly in IT …

Reduce Cost at Scale with Automated Governance & Guardrails
Reduce Cost at Scale with Automated Governance & Guardrails Background As organisations …
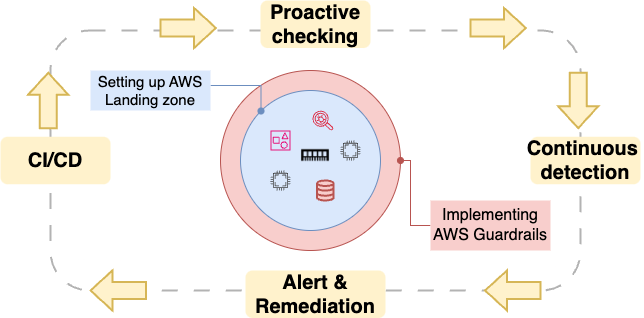
Why organisations should implement AWS Landing Zone and Guardrails?
In a fast-paced cloud environment governance is fundamental, defining standard policies for …
AWS NLB and Client IP Preservation - How to create Security Group Rules
Have you ever created a Network Load Balancer on AWS, its target group and its target, and some …
Break the rules of virtualization, build Lambdas container images for any platform, from any platform, with CDK & Docker buildx
How often are you deploying a Lambda container image, basically a Lambda running on a Docker image, …
AWS CDK + API Gateway and Integrations. A little guide how to.
I’ve been working with CDK and I think is brilliant, the way it lets you define resources and …
Simply Deploy AWS IAM Identity Center Permission Sets with Ezpresso
With AWS IAM Identity Center, formerly known as AWS Single Sign-On, it became simpler to integrate …
Enable Security Hub in an AWS Organization
Background In November 2020 AWS announced that Security Hub now integrates with AWS Organizations. …
Use the Raspberry Pi 4 for AWS development - Part 1, Installation
Background With the advent of the Raspberry Pi 4, Pi’s are sufficiently powerful in terms of …
Get started with Ubuntu 20.04 on Raspberry Pi 4
Background With the advent of the Raspberry Pi 4, Pi’s have become quite powerful both in CPU …
Install & run AWS Glue 1.0 and PySpark on Ubuntu 20.04
Background It’s much faster to be able to develop and debug AWS Glue / PySpark scripts …
Leveraging Serverless (SAM) with Cognito Authentication
Introduction Using Serverless combined with Cognito can be a great way to eliminate the real estate …
The case for Structured, Contextual Logs
Introduction If correctly composed, logs can be an extremely useful resource to tap into in the …
6 Steps to DevOps
Introduction Why adopt DevOps? IT change can be painful and subject to long lead times in many …
Why Serverless & DevOps makes a (big) difference
Background We have recently completed a Serverless & DevOps transformation project with one of …
Moving to Cloud: the Landing Zone
In military terms a Landing Zone is an area where aircraft can land; in effect a base camp from …
Securing Cross-Account AWS API Calls & CLI Access with MFA (Two-Factor) Authentication
AWS Cross-Account Roles are an excellent way of managing access to a target account (the account in …
Creating a Core Network Foundation in AWS with SSH, VPN & NAT access
For both test and build purposes I often find myself reusing parts of past CloudFormation templates. …
Need a good reason to switch to Cloudformation YAML now? Template size limits…
AWS CloudFormation size limits are well-documented in the User Guide. However, this does not make …
Moving to Cloud: Agility
Over the years I have witnessed, proposed and implemented a wide range of AWS use cases; and few of …
Securing AWS API Calls & CLI Access with MFA (Two-Factor) Authentication
One of the largest concerns of allowing AWS API calls to be made from the outside is issuing an API …